Quick Links
Yahoo Launches Identity Solutions For CTV, Bridging the...
Singapore, 22 April 2024 – Yahoo Advertising is launching Yahoo Identity Solutions for connected TV (CTV) environments, including Paramount. The move will see Yahoo ConnectID and Next-Gen Solutions products made…
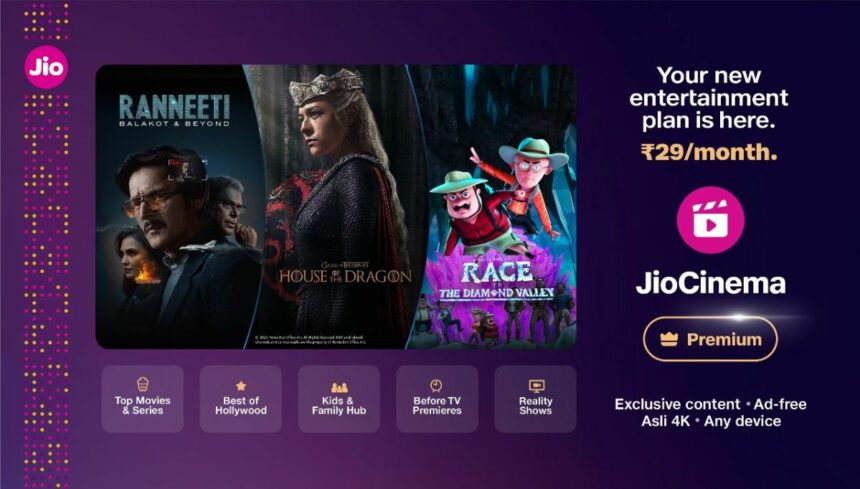
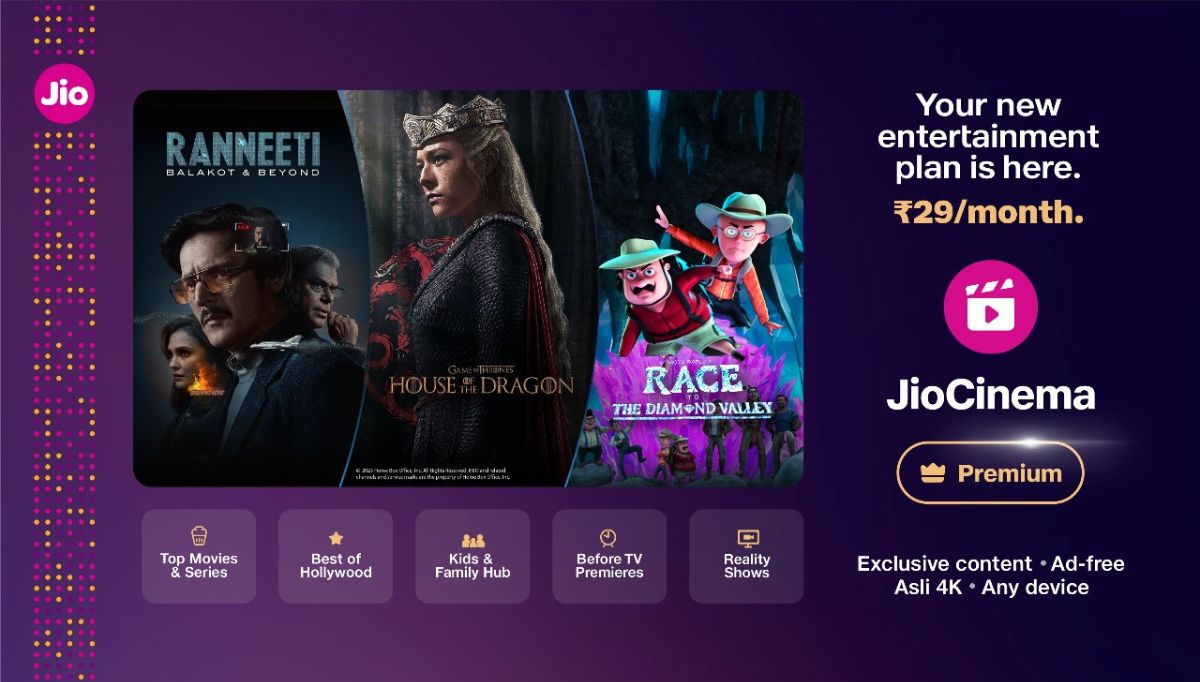
JioCinema set to redefine subscription market with laun...
~ Special introductory pricing of Rs. 29/month for any single device and Family plan at Rs. 89/month for up to any 4 devices ~ ~Enhanced viewing experience with 4K Ad-free…
Uniting Strengths: Matthias Bertl, Managing Director at...
The furniture fittings industry is witnessing a significant transformation as Hettich, a global leader with over 135 years of experience, completes its acquisition of FGV. This union brings together two…
Editor's Pick
OpenMinds Group Names Female Leaders to Drive OpenMinds...
OpenMinds Group, a leading Southeast Asian MarTech company, announced today the launch…
Most Read
Australian Women in Business Excellence Awards Winners
Latest News
Southeast Asia marketers set to prioritise investment i...
Advertising spend on Retail Media Networks (RMNs) in Southeast Asia is projected…
Billboards Reborn: A Modern Marketing Powerhouse in Mal...
Forget the dusty image of static billboards lining highways. In Malaysia’s dynamic…
Swiggy Launches Smart Links to Boost Restaurant Growth ...
Swiggy, a leading online food ordering and delivery service, has introduced 'Smart…
Goafest 2024 Unveils the Festival Theme – ‘The ...
The Advertising Agencies Association of India (AAAI) and The Advertising Club are…
Cancer Chicks launches provocative new brand platform �...
Sydney. April 24, 2024: Charity organisation, Cancer Chicks has launched a powerful new brand platform and campaign, FUCC It, aimed to get Australians en masse, talking about and supporting young…
Azleen Abdul Rahim
320 Articles
I write about marketing strategy, entrepreneurship and life.
Dr. Surbhi Sharma
752 Articles
I am PhD in Mathematics from IIT Roorkee currently working as a Market Research & Data Analyst. I have a demonstrated history of working with…